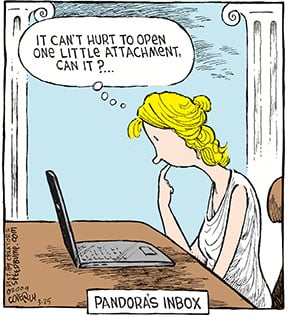
Email scams are an inevitable part of living in a digital age. The most deceptive appear as inquiries, warnings or attachments from a trusted friend, colleague or organization like your local church. In truth, imposters are tricking people to reveal contacts, confirm logins or reset personal information.
Has your information been harvested by a data breach? Use this tool to check. Prevent further data hijacking by minding these tips.
How does it happen?
“In the past, listing contact information on the church website offered accessibility for people seeking a connection with their local churches,” says Danny Mai, United Methodist Communication’s (UMCom) chief operating officer. “However, these listings are also prime data sources for people with nefarious intent.”
Is it secure?
Email addresses displayed publicly on Facebook or a website are easily scraped by spammers and scammers looking to impersonate legitimate email addresses. Compromised email addresses need to be changed immediately. As a caution, publicly listed email addresses should be changed routinely. Fortunately, you can maintain security and privacy without losing the personal touch.
To protect your public online listings, consider these countermeasures, ranked from low tech to coder level and one UMCom recommends.
Use a burner email address
Keep your real email address private by sharing it only with people you know and never posting or linking to it publicly. For public listings, use a disposable single-use email address (a burner) that can be abandoned at the first sign of concern, whether that’s an increase in spam or suspicion of a hack. For added security, use a generic address (i.e. [email protected]) to avoid revealing your name.
Establish an alias
Feel like a spy yet?! Gmail users can create aliases to fool shady impersonators by adding +[any text or alias name you choose] to email addresses. For example, [email protected] would become an alias for [email protected]. Use the alias to sign up for whitepapers and e-newsletters (other than MyCom 😉 ) or to list on your website. Email sent to an alias is delivered to the legitimate inbox (in our example, [email protected]) but can be automatically redirected through email settings to a separate folder for later review or to the trash. If an alias is compromised, create a new one and block emails to the original.
Display @ as [at]
Email addresses always include the @ symbol, so that’s what email scrapers are programmed to search for across websites. Replace the symbol with [at], i.e. church[at]email.org, to fight against most scrapers. Consider the impact this may have on community contacts prior to implementing this as they may not recognize what you’ve done. The burner or alias tactic may be more appropriate for your church.
Hyperlink to disguise
Instead of exposing email addresses on your website, hyperlink titles of your leaders to mask their email addresses until appearing in the “to” field of a new message. For example, “Contact Senior Pastor” displays as a clickable link. Behind it is the code to trigger an email to “mailto:[email protected]”. While it’s not foolproof against scraper software, it creates a barrier.
Add a contact form (UMCom’s top recommendation)
The Find A Church tool hosted by United Methodist Communications assures privacy through use of a “Contact Church” form. Messages submitted to a church listed on Find A Church trigger an email to a designated church representative.
Forms are simple to create and make church contact information entirely anonymous. Many, if not most, website platforms offer contact form builders. If yours doesn’t, look to tools like JotForm for one to embed to your website.
Use CSS or Javascript
For the coder, an old-hat CSS trick reverses an email address by overriding the text direction. For example, note the first line below, which is a sample email address ([email protected]) displaying backward as “moc.hcruhc@elpmaxe.”
<span class=“reverseemail”>moc.hcruhc@elpmaxe</span>
<style>
span.reverseemail{
unicode-bidi: bidi-override;
direction: rtl;
}
</style>
Once Javascript (see sample below) is applied, the email address reassembles in the correct order for the screen view while the code behind it (often what the scrapers are programmed to comb through) remains unreadable.
.emailhider:after {
content: attr(data-name) "@" attr(data-domain) "." attr(data-tld);
}
<a href="#" class="emailhider”
data-name=“example”
data-domain=“church”
data-tld="org"
onclick="window.location.href = 'mailto:' + this.dataset.name + '@' + this.dataset.domain + '.' + this.dataset.tld; return false;"></a>
Like what you're reading and the tools we provide?
“Don’t get a false sense of security with this trick” says Lane Denson, UMCom’s senior manager of web development. “Many scrapers today are sophisticated enough to look at both the code and the rendered page that displays the email address correctly. The bottom line is if an email address is displayed in full on a page, it can be scraped. ”
Whether you’re ready to jump into coding or only commit to a burner email address, it’s possible to stop many email scams before they begin. Start by auditing the places where email addresses are public and edit them immediately using one or more of the tips covered. Advise your church leaders and members of the dangers of leaving email addresses public.
Vow to make 2021 the year of greater privacy and security.

Jeremy Steele is the associate pastor at Los Altos UMC in Los Altos, California, as well as a writer and speaker. You can find a list of all his books, articles and resources for churches, including his most recent book All the Best Questions, at his website: JeremyWords.com.

